Advanced Search
Content Type: News & Analysis
We’ve been asked a lot lately about whether it is safe to travel, particularly to the US. And it’s not surprising why: the US Government is increasing their cruelty at borders.Border management today is fueled by our data, but government officials want more. They want as much data as they can get to catch you out. They’ve reportedly detained or deported people based on their free speech activities, denying entry on tenuous grounds like having the wrong photos on phones (including in in the ‘…
Content Type: Long Read
It’s important to us at PI that we continue to create real change in the world. We want our work to matter, and we challenge ourselves continuously to verify that it does.In 2024 we made substantial progress towards concrete systemic change. We challenged governments and corporations that exploit data and technology, pushed for new national and international policy standards, drove standard-setting action by courts and regulators. We educated and campaigned with others.As a result, we produced…
Content Type: News & Analysis
On 11 March 2025, The Atlantic journalist, Jeffrey Goldberg was added to a Signal chat where senior US Government officials were discussing the United States’ military strikes in Yemen.This happened to Goldberg as an accident. Yet, security services around the world have pushed for this to be part of their clandestine surveillance operations: the so-called “Ghost Protocol”.Governments have been trying to gain access to private online conversations since private online conversations have existed…
Content Type: Long Read
In 2024, Privacy International (PI) continued to produce real change by challenging governments and corporations that use data and technology to exploit us.Since the beginning of the year, we’ve achieved some wins and would like to share the most recent ones with you.Creating change is hard, and takes time. We have to uncover problems, draw attention to them, and pressure for change. In the latest quarter, we've been able to push regulators for stronger standards on generative AI systems, draw…
Content Type: Long Read
On 13 March 2025, we filed a complaint against the UK government challenging their use of dangerous, disproportionate and intrusive surveillance powers to undermine the privacy and security of people all over the world. Here, we answer some key questions about the case and the recent events that led to this development.Note: This post was last updated on 13 March 2025.What’s the fuss about?A month ago, it was reported that the UK government demanded Apple Inc – maker of the iPhone, iPads, Macs…
Content Type: Explainer
Imagine this: a power that secretly orders someone anywhere in the world to abide and the receiver can’t tell anyone, can’t even publicly say if they disagree, and can’t really question the power in open court because the secret order is, well, secret. Oh and that power affects billions of people’s security and their data. And despite being affected, we too can’t question the secret order.In this piece we will outline what’s ridiculous, the absurd, and the downright disturbing about what’s…
Content Type: News & Analysis
Edit: 13 March 2025 - You can find more about what happened next on our case pageOn February 21st, Apple disabled their ‘advanced data protection’ service for UK customers. That means no-one in Great Britain can now enable a powerful security safeguard that people who use Apple devices everywhere else on the planet can: user controlled end-to-end encryption of stored data.This is likely in response to a disturbing secret government power. Well, that’s what we think happened. We can’t know for…
Content Type: Guide step
Depending on where in the world you are visiting from, websites may seek consent as one way to justify their collection of data about you. This has become general practice across the web, and the typical way to ask for user consent is via banners that pop up first thing when the webpage loads. Often these banners will make use of design elements and user interfaces aiming to mislead or influence you in giving away consent to collect and process your data - these are called Dark Patterns and are…
Content Type: Press release
Privacy International (PI)FOR IMMEDIATE RELEASEUnited Kingdom goes after Apple's encrypted dataThe United Kingdom has used its investigatory powers to force disclosure of private data held by Apple Inc."The United Kingdom's unprecedented attack on individuals' private data around the globe is disproportionate and unnecessary.""This is a fight the UK should not have picked. The reported details suggest the UK is seeking the ability to access encrypted information Apple users store on iCloud, no…
Content Type: Advocacy
Our joint stakeholder report made the following recommendations: Strengthen the implementation of Data Protection Act, 2019 and make clear in law and in relevant guidelines that personal data from the electoral register which has been made accessible is still subject to, and protected, by data protection law, including for onward processing.Ensure that there is an effective legal and regulatory framework in place to guarantee a human rights-based approach in the design and deployment of…
Content Type: Advocacy
Our submission made the following recommendations to the Committee regarding the Kenya:Review and amend the proposed digital identity system, the Maisha Numba, to ensure it aligns with Kenya’s national and international human rights obligations in its design and implementation, and adopts legal, policy and technical safeguards to prevent exclusion and marginalisation.Ensure that measures taken to develop digital public infrastructures abide by Kenya’s national and international human rights…
Content Type: Video
Links- Read PI's research- Learn more about Rhizomatica- Learn more about Lũa and his work on Starlink- We'd love to hear from you! Share your thoughts, case studies, or ideas about vertical mergers using our survey- More about X and Starlink's legal trouble in Brazil- Our podcast about competition with Dr Deni Mantzari
Content Type: Advocacy
We responded to the Home Office consultation on codes of practices under the Investigatory Powers (Amendment) Act 2024 (IPAA). Our response focused on (1) the draft codes relating to bulk personal datasets with low or no reasonable expection of privacy, (2) third-party bulk personal datasets and (3) the notices regime. You can download our full response with its 23 recommendations for reform at the bottom of this page.'Low Privacy' Bulk Personal DatasetsThe IPAA introduces a new concept of…
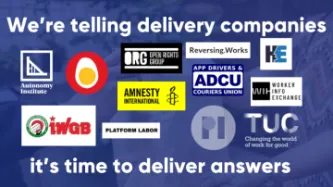
Content Type: News & Analysis
Together 12 organisations, including trade unions and NGOs across the EU and the UK, are asking Deliveroo, Uber, and Just Eat Takeaway to take serious steps to significantly improve the transparency and explainability around the algorithms they use to manage their workforce.These platforms rely heavily on the use of algorithms to manage many aspect of their workers employment, from account creation, to account suspension to how much workers get paid. Yet, it’s almost impossible for workers to…
Content Type: Advocacy
Algorithmic management of workers has become the norm for gig-economy platforms, with workers obligated to give up an immense amount of personal data just to go to work. Decisions made by these algorithms can determine how much individuals are paid and even whether their employment or accounts are suspended or terminated. Yet, workers are often not provided with satisfactory explanations as to how these decisions are made. This lack of transparency means that decisions made through the "black-…
Content Type: Long Read
Intrusive surveillance technology is increasingly used during protests around the world, and we’ve been tracking its use around the world for years.This technology is often being deployed in secret, without a clear legal basis and without the safeguards and oversight applied to other surveillance technologies under international human rights law.We’ve increasingly observed the use of unlawfully generated and collected data from these technologies being used in court against people exercising…
Content Type: Long Read
What happened?On 19 July 2024, American cybersecurity company CrowdStrike released an update to its CrowdStrike Falcon software that ultimately caused 8.5 million computers running Microsoft Windows to crash. The damage done was both deep and wide: deep because the computers affected were unable to recover without direct user intervention. Wide because a whole range of companies - from airlines to healthcare to media - across a whole range of countries - from Sweden to India to New Zealand -…
Content Type: Long Read
In 2019, the Waorani achieved a huge legal victory against the Ecuadorian government. They opposed the sale of millions of hectares of their rainforest to new oil companies, a forest that forms part of the home and territory of seven different Indigenous peoples in the southern Ecuadorian Amazon. Nemonte Nenquimo, as the first female leader of the Waorani of Pastaza and co-founder of the nonprofit Alianza Ceibo, and plaintiff in this case, has been a powerful advocate for her community’s…
Content Type: Examples
On behalf of the Norwegian government, the Norwegian Intelligence Service has awarded Kongsberg Defence and Aerospace (“Kongsberg”) a four-year contract to supply satellite maritime surveillance data in order to cover Norwegian Areas of Interest. Kongsberg will produce three satellites and equip them with automatic identification system receivers and detector systems; the data will be used by the Norwegian Armed Forces and other Norwegian government bodies. Kongsberg will be the owner of the…
Content Type: Examples
Westminster Group PLC has ratified a ten-year, multi-million-pound contract to supply ground security operations and advanced detection, surveillance, and screening equipment, as well as maintenance, training, and support at one domestic and four international airports in the Democratic Republic of the Congo (DRC). Under the managed services model, which Westminster has deployed elsewhere in Africa, revenues will be driven by embarking passenger numbers and funded by a fee per passenger…
Content Type: Examples
As part of an agreement worth up to $20.8 million, Teledyne FLIR Defense will deliver ultra long-range multi-spectral imaging surveillance systems, or Star SAFIRE 380-HLD, to the Japan Maritime Defense Force, which will integrate them into the licenced Japan-based production version of the Sikorsky SH-60 helicopter. The system can operate continuously in all weather conditions and can transmit both thermal and visual imagery in high definition to those who are operating it. https://www.…
Content Type: Examples
The Swedish Defence Materiel Administration has awarded Saab a $245 million contract to provide the Swedish air force with a third GlobalEye surveillance aircraft and other services like those already in use in UAE. The contract runs until 2029. The air force is accelerating the schedule for introducing locally-designated assets after donating its current two Erieye radar-equipped Saab 340 early warning and control aircraft to Ukraine. https://www.flightglobal.com/defence/sweden-signs-…
Content Type: Examples
The US Air Force will give Capella Space Corp $15 million in funding to improve and scale its synthetic aperture radar to deliver enhanced resolution imagery. Capella also supplies technology to the National Geospatial Intelligence Agency, National Reconnaissance Office, US Navy, US Space Force, and NASA.https://www.capellaspace.com/press-releases/capella-space-awarded-a-15m-contract-with-the-u-s-air-forcePublication: Capella SpaceWriter: Capella Space
Content Type: Examples
It has been announced that the California Highway Patrol has signed a $1.6 million (for the first year) contract with Flock Safety to install 480 high-tech cameras on Oakland's streets and freeways to identify licence plates and catalogue passing vehicles by make, model, colour, and other features. An official asserted that footage obtained from the cameras would be deleted after 28 days and not shared with third parties or other states that might use the information to track people seeking or…
Content Type: Examples
The UK Home Office has renewed its 3 year long contract with Tekever to provide maritime surveillance as a service across the English Channel using its AR5 and AR3 model drones, also known as Unmanned Aerial Vehicles (UAVs). The AR5 system is a UAV that is intended to conduct surveillance missions and can fly for more than 20 hours and carry sensors such as maritime radar and day and night cameras. It will be used to detect, recognise, track, and identify potentially illegal vessels and…
Content Type: Examples
Under a new contract, Planet Labs PBC will provide the NATO Communications and Information Agency's Alliance Persistent Surveillance from Space programme (APSS) with satellite data to aid in detailed tracking and analysis of foreign military activities and fill intelligence gaps. APSS is a multi-year, multinational project to use space to collect data on any location at any time and enhance NATO's engagement with future technologies, for example Artificial Intelligence (AI) and cloud…
Content Type: Examples
The US Department of Defense has awarded a contract worth almost $250 million to Anduril Industries for more than 500 Roadrunner-Ms as well as Pulsar electronic warfare capabilities, with AI-enabled systems, to counter the threat of attacks using unmanned aerial systems in “priority regions”. Anduril has won nearly $350 million in contracts since these technologies were publicly launched.https://www.designdevelopmenttoday.com/industries/military/news/22922589/anduril-awarded-250-million-air-…
Content Type: Examples
Under a new contract effective from October 2024 to December 2025, PureTech Systems, which specialises in geospatial AI-boosted video analytics, will deploy its command-and-control software in 22,600 square kilometers of the US border. The software will integrate the sensors attached to existing surveillance towers while retaining the interface already familiar to border agents.https://www.prnewswire.com/news-releases/puretech-systems-inc-awarded-major-command-and-control-contract-by-us-…