Advanced Search
Content Type: Long Read
What happened?On 19 July 2024, American cybersecurity company CrowdStrike released an update to its CrowdStrike Falcon software that ultimately caused 8.5 million computers running Microsoft Windows to crash. The damage done was both deep and wide: deep because the computers affected were unable to recover without direct user intervention. Wide because a whole range of companies - from airlines to healthcare to media - across a whole range of countries - from Sweden to India to New Zealand -…
Content Type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.
It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content Type: Press release
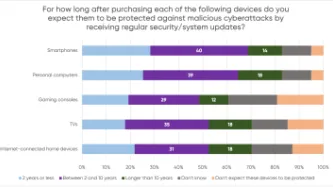
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content Type: Advocacy
On 30 March 2022, the European Commission published a proposal for a directive empowering consumers for the green transition, which is is designed to enhancing consumer rights in making informed choices in order to play an active role in the transition to a climate-neutral society. At the moment, the proposal is being discussed by the Committee on the Internal Market and Consumer Protection of the European Parliament.
PI welcomes the aim of the proposal to enhance consumer rights, particularly…
Content Type: Explainer
With more and more connected devices around us, the chance that you've been hit by an update notification is high. But what do these software updates do? How do they actually work, and why are they important?
Hardware and Software
Modern electronic devices require two main parts to function: the hardware and the software. The hardware usually refers to physical electronic pieces inside a device (usually a collection of microchips, logic gates and specialised processing chips, such as those to…
Content Type: Advocacy
Our environment is increasingly populated by devices connected to the Internet, from computers and mobile phones to sound systems and TVs to fridges, kettles, toys, or domestic alarms. There has been research into the negative safety and privacy impacts of inadequate security provided by the software in such devices (such as the creation of large scale botnets). This is also the case with outdated security, a risk enabled by software support periods that are shorter than a product’s usable life…