Advanced Search
Content Type: Video
Please note the views expressed in the video are the interviewee's own and do not necessarily reflect the views of PI.
Driver X (he wishes to remain anonymous) has been working for Uber for five years. After working for Uber for two and half years, he suddenly received a message telling him that his account had been temporarily suspended and asking him not to call Uber while the investigation was pending. He was baffled, as he had an excellent record and rating, with plenty of positive…
Content Type: Long Read
What if your boss was an algorithm? What would you do if your employer suddenly fired you or reduced your pay without telling you why? And without being willing to give you a reason when you ask for one?
This is not science fiction or some far-fetched reality. Millions of people worldwide are working in the gig economy sector for companies like Uber, Deliveroo, Bolt, Just Eat… And this could be the future of work for people working outside the gig economy, as surveillance technologies are…
Content Type: Video
Update: Pa has since won a settlement from UberPlease note the views expressed in the video are interviewee's own and do not necessarily reflect the views of PI.Pa used to work for Uber. After some time, Uber started asking him to submit a picture of himself to the platform to confirm it was indeed him who had completed the job. However, with time, the frequency of the requests increased. In the beginning, the requests for a picture only happened once a week, but as time went by Pa told us that…
Content Type: News & Analysis
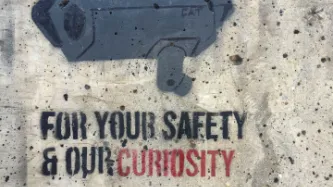
What if we told you that every photo of you, your family, and your friends posted on your social media or even your blog could be copied and saved indefinitely in a database with billions of images of other people, by a company you've never heard of? And what if we told you that this mass surveillance database was pitched to law enforcement and private companies across the world?
This is more or less the business model and aspiration of Clearview AI, a company that only received worldwide…
Content Type: Video
<br />
Links
Read more about the ICO's provisional decision
Support our work
You can find out more about Clearview by listening to our podcast: The end of privacy? The spread of facial recognition
Content Type: Press release
In what could be seen as one of the strongest sanctions against the company in Europe, the Information Commissioner’s Office (ICO), which is tasked with enforcing data protection legislation in the UK, has today announced its provisional intent to issue a potential fine of £17 million against the controversial facial recognition company Clearview AI.
Clearview AI, which only received worldwide attention following a New York Times report back in January 2020, is a company whose business model…
Content Type: Advocacy
The Office of the Privacy Commissioner of Canada has developed draft privacy guidance for police agencies' use of FRT, with a view to ensuring any use of FRT "complies with the law, minimizes privacy risks, and respects privacy rights". The Commissioner is undergoing consultation in relation to this guidance.
Privacy International and the Canadian Civil Liberties Association ("CCLA") welcome the Commissioner's efforts to strengthen the framework around police use of facial recognition, and the…
Content Type: Advocacy
Our environment is increasingly populated by devices connected to the Internet, from computers and mobile phones to sound systems and TVs to fridges, kettles, toys, or domestic alarms. There has been research into the negative safety and privacy impacts of inadequate security provided by the software in such devices (such as the creation of large scale botnets). This is also the case with outdated security, a risk enabled by software support periods that are shorter than a product’s usable life…
Content Type: Advocacy
On 6 August 2021, the World Health Organisation (WHO) published its technical specifications and implementation guidance for “Digital Documentation of COVID-19 Certificates: Vaccination Status” (DDCC:VS) following months of consultations. As governments around the world are deploying their own Covid-19 certificates, guidance from the global health agency was expected to set a global approach, and one that prioritises public health. As such, we would expect the WHO to identify what these…
Content Type: News & Analysis
Today Apple announced a set of measures aimed at improving child safety in the USA. While well-intentioned, their plans risk opening the door to mass surveillance around the world while arguably doing little to improve child safety.
Among the measures, Apple has announced that it is to introduce “on-device machine learning” which would analyse attachments for sexually explicit material, send a warning, and begin scanning every photo stored on its customers’ iCloud in order to detect child…
Content Type: Long Read
Additionally, in January 2020 Privacy International and UK-based NGO Liberty filed a new claim against MI5 and the Secretary of State for the Home Department in the Investigatory Powers Tribunal (the “Ungoverned Spaces Case”, this time, the case sought to hold MI5 and the SSHD accountable for systemic, long-term failures in the way they handle and retain millions of people’s personal data. As part of this claim, PI requested that the IPT re-opens parts of the original BPD/BCD. This aspect of…
Content Type: News & Analysis
What happened
On 22 July 2021, the Investigatory Powers Tribunal (IPT) issued a declaration on our challenge to the UK bulk communications regime finding that section 94 of the Telecommunications Act 1984 (since repealed by the Investigatory Powers Act 2016) was incompatible with EU law human rights standards. The result of the judgment is that a decade’s worth of secret data capture has been held to be unlawful. The unlawfulness would have remained a secret but for PI’s work.
You…
Content Type: News & Analysis
It is difficult to imagine a more intrusive invasion of privacy than the search of a personal or home computer ... when connected to the internet, computers serve as portals to an almost infinite amount of information that is shared between different users and is stored almost anywhere in the world.
R v Vu 2013 SCC 60, [2013] 3 SCR 657 at [40] and [41].
The controversial Police Crime Sentencing and Courts Bill includes provision for extracting data from electronic devices.
The Bill…
Content Type: Long Read
Photographing or filming incidents involving police and protestors is an important way of holding the police to account for their actions. Members of the public and the media do not need a permit to film or photograph in public places and police have no power to stop them filming or photographing incidents or police personnel.[1]
Can the police stop and search me for filming or taking photographs?
The police have the discretion to ask you to move back if they think you are interfering with…
Content Type: Long Read
The Grand Chamber of the European Court of Human Rights ruled that the UK government’s historical mass interception program violates the rights to privacy and freedom of expression. The Court held that the program “did not contain sufficient “end-to-end” safeguards to provide adequate and effective guarantees against arbitrariness and the risk of abuse.” As a result the Court ruled that UK law "did not meet the “quality of law” requirement and was therefore incapable of keeping the “…
Content Type: Long Read
On 25 May 2021, the European Court of Human Rights issued its judgment in Big Brother Watch & Others v. the UK. Below, we answer some of the main questions relating to the case.
After our initial reaction, below we answer some of the main questions relating to the case.
NOTE: This post reflects our initial reaction to the judgment and may be updated.
What’s the ruling all about?
In a nutshell, one of the world’s most important courts, the Grand Chamber of the European Court of Human…
Content Type: Press release
The Grand Chamber of the European Court of Human Rights has today ruled that UK mass surveillance laws violate the rights to privacy and freedom of expression.
It found that:
The UK’s historical bulk interception regime violated the right to privacy protected by Article 8 of the European Convention on Human Rights and freedom of expression, protected by Article 10. Particularly it found that:
the absence of independent authorisation,
the failure to include the categories of selectors…
Content Type: Press release
Privacy International (PI), together with Hermes Center for Transparency and Digital Human Rights, Homo Digitalis and noyb - the European Center for Digital Rights, has today filed a series of legal complaints against Clearview AI, Inc. The facial recognition company claims to have “the largest known database of 3+ billion facial images”. The complaints were submitted to data protection regulators in France, Austria, Italy, Greece and the United Kingdom.
As our complaints detail, Clearview AI…
Content Type: News & Analysis
The Aspen Card - the debit payment card given to asylum seekers that PI has previously exposed as a de facto surveillance tool - will be outsourced to a new company. The contract with Sodexo has come to an end and the company Prepaid Financial Services will be taking over.
Our campaign for transparency in relation to the Aspen Card and how it monitors asylum seekers continues. Not only do we demand clarity from the Home Office [read more here], we believe the new provider, Prepaid Financial…
Content Type: Explainer
What is social media monitoring?
Social media monitoring refers to the monitoring, gathering and analysis of information shared on social media platforms, such as Facebook, Twitter, Instagram and Reddit.
It may include snooping on content posted to public or private groups or pages. It may also involve “scraping” – grabbing all the data from a social media platform, including content you post and data about your behaviour (such as what you like and share).
Through scraping and other tools…
Content Type: Explainer
What are my 'unique identifiers' and where are they stored?
Your phone and your SIM card contain unique identifiers about you, which can be accessed by the police to identify you.
The IMSI (International Mobile Subscriber Identity) is a unique number associated with your SIM card. It doesn't change, even if you put the SIM card into a different phone.
If you have a mobile phone subscription, the IMSI will be associated with personal information such as your name and address.
The IMEI (…
Content Type: Explainer
Where are my communications stored?
Text messages/phone calls: Traditional cellphone communications happen over the cellular network. You usually access those with the text message and phone call apps that are provided as standard on your phone. While phone calls aren’t stored anywhere, text messages are stored locally on your and the recipient’s devices. They might also be temporarily stored by the network provider.
Messaging apps: Messaging platforms enable fairly secure communication…
Content Type: Explainer
Where is my phone's location data stored?
Your phone can be located in two main ways, using GPS or mobile network location:
1. GPS
GPS (that stands for Global Positioning System) uses satellite navigation to locate your phone fairly precisely (within a few metres), and relies on a GPS chip inside your handset.
Depending on the phone you use, your GPS location data might be stored locally and/or on a cloud service like Google Cloud or iCloud. It might also be collected by any app that you…
Content Type: Explainer
What is predictive policing?
Predictive policing programs are used by the police to estimate where and when crimes are likely to be committed – or who is likely to commit them. These programs work by feeding historic policing data through computer algorithms.
For example, a program might evaluate data about past crimes to predict where future crimes will happen – identifying ‘hot spots’ or ‘boxes’ on a map. But the data these programs use can be incomplete or biased, leading to a ‘feedback…
Content Type: Explainer
What is LEDS?
LEDS is a new mega-database currently being developed by the UK Home Office.
LEDS will replace and combine the existing Police National Database (PND) and the Police National Computer (PNC). The aim is to provide police and others with a super-database, with on-demand, at the point of need access, containing up-to-date and linked information about individuals’ lives.
Once your details are in LEDS, numerous agencies will have access to that information (e.g. HMRC and DVLA),…
Content Type: Explainer
What are police drones?
Drones are remotely controlled Unmanned Aerial Vehicles (UAVs) of varying sizes.
They usually come equipped with cameras and might be enabled with Facial Recognition Technology.
Drones can be equipped with speakers, surveillance equipment, radar and communications interception tools, such as ‘IMSI catchers’.
How might drones be used during protests?
Camera-enabled drones may be used to remotely monitor and track people’s movements in public spaces, including at…
Content Type: Explainer
What do Body Worn Video cameras do?
Body worn video (BWV) cameras can be attached to a police officer’s clothing – often at chest, shoulder or head level – and record video, including sound, from the officer’s perspective.
BWV cameras will probably be visible to you, and when it’s recording, a flashing light should appear on the device.
How might body worn video cameras be used at a protest?
BWV cameras may be used at protests to monitor actions of protestors.
They do not usually…
Content Type: Explainer
What is gait recognition technology?
Gait recognition technology (GRT) can analyse the shape of an individual’s body and the unique way in which that body moves when walking or running, which can then be used to identify them.
GRT works in a similar way to facial recognition technology. But the two main differences are:
GRT may be used at a fairly long range (at the time of writing, about 165 feet / 50 metres), unlike FRT which generally requires more close up, detailed facial images…
Content Type: Explainer
What is Facial Recognition Technology?Facial recognition technology (FRT) collects and processes data about people’s faces, and can be used to identify people. FRT matches captured images with images stored in existing databases or ‘watchlists’.How might it be used in relation to a protest?FRT may be used to monitor, track and identify people’s faces in public spaces, including at protests. This may be done openly or surreptitiously, without people knowing or consenting.FRT-enabled cameras can…
Content Type: Explainer
What is hacking?
Hacking refers to finding vulnerabilities in electronic systems, either to report and repair them, or to exploit them.
Hacking can help to identify and fix security flaws in devices, networks and services that millions of people may use. But it can also be used to access our devices, collect information about us, and manipulate us and our devices in other ways.
Hacking comprises a range of ever-evolving techniques. It can be done remotely, but it can also include physical…