Advanced Search
Content Type: Video
In Kenya, if you don’t have an ID, life can be extremely difficult. But for thousands of people across the country, getting an ID can be nigh on impossible. Some Kenyan citizens can’t obtain a national ID because they are registered in the Kenyan refugee database. Often referred to as victims of double registration, their predicaments reveal a deeper problem with ID itself.
Now Haki na Sheria - a Kenyan organisation advocating for and supporting the victims of double registration - and three…
Content Type: Long Read
Governments around the world are increasingly making registration in national digital ID systems mandatory for populations, justifying its need on a range of issues from facilitating access to services, to national security and fighting against corruption. This is an attempt to create a "foundational identity" for an individual, or "a single source of truth" about who someone is, according to a government agency. These identity systems are run by governments, sometimes by private companies, or…
Content Type: Advocacy
Some of the most vulnerable groups in Mexico are amongst the groups at risk from a draft General Population Law that creates a biometric “Unique Digital Identity Card” (CUID), argue civil society organisations. The proposed law has now reached the senate, and has raised serious concerns from civil society organisations. Led by our global partner in Mexico Red en Defensa de los Derechos Digitales (R3D), PI along with 25 organisations have signed a joint letter to the members of the senate,…
Content Type: News & Analysis
After almost 20 years of presence of the Allied Forces in Afghanistan, the United States and the Taliban signed an agreement in February 2020 on the withdrawal of international forces from Afghanistan by May 2021. A few weeks before the final US troops were due to leave Afghanistan, the Taliban had already taken control of various main cities. They took over the capital, Kabul, on 15 August 2021, and on the same day the President of Afghanistan left the country.
As seen before with regime…
Content Type: Advocacy
On 6 August 2021, the World Health Organisation (WHO) published its technical specifications and implementation guidance for “Digital Documentation of COVID-19 Certificates: Vaccination Status” (DDCC:VS) following months of consultations. As governments around the world are deploying their own Covid-19 certificates, guidance from the global health agency was expected to set a global approach, and one that prioritises public health. As such, we would expect the WHO to identify what these…
Content Type: News & Analysis
This article was written by Abdías Zambrano, Public Policy Coordinator at IPANDETEC, and is adapted from a blog entry that originally appeared here.
Digital identity can be described as our digital personal data footprint, ranging from banking information and statistics to images, news we appear in and social network profiles, interactions with and in digital platforms, and information contained in private and public repositories. Our whole life is online, often leaving us with little choice…
Content Type: News & Analysis
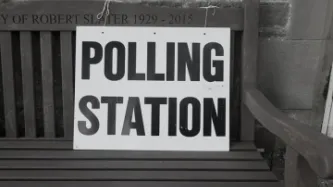
Legislation to "strengthen the integrity of UK elections and protect our democracy" through the Elections Integrity Bill was introduced to parliament this week.
This legislation will require people, for the first time in Great Britain, to show a state-issued photo ID, such as a driving license or passport, in order to exercise their right to vote, perhaps by the 2023 General Elections. The changes would affect elections in England, Scotland and Wales while voters in Northern Ireland are already…
Content Type: News & Analysis
Today, the UK High Court has quashed a decision by the Investigatory Powers Tribunal (IPT) and held that section 5 of the Intelligence Services Act (ISA) 1994 does not permit the issue of general warrants to authorise property interference and certain forms of computer hacking.
The Court referred to cases dating back to the 18th century, which demonstrate the common law’s insistence that the Government cannot search private premises without lawful authority even in the national security…
Content Type: Press release
Today, the UK High Court has quashed a decision by the Investigatory Powers Tribunal (IPT), and ruled that section 5 of the Intelligence Services Act (ISA) 1994 does not permit the issuing of general warrants to authorise property interference and certain forms of computer hacking.
The Court referred to cases dating back to the 18th century, which demonstrate the common law’s insistence that the Government cannot search private premises without lawful authority even in the context of national…
Content Type: Report
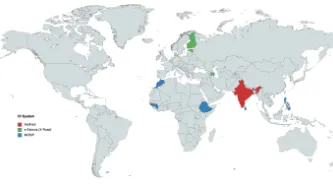
Many countries in the world have existing ID cards - of varying types and prevalence - there has been a new wave in recent years of state “digital identity” initiatives.
The systems that states put in place to identify citizens and non-citizens bring with them a great deal of risks.
This is particularly the case when they involve biometrics - the physical characteristics of a person, like fingerprints, iris scans, and facial photographs.
Activists and civil society organisations around the…
Content Type: Report
A common theme of all major pieces of national jurisprudence analyzing the rights implications of national identity system is an analysis of the systems’ impacts on the right to privacy.
The use of any data by the State including the implementation of an ID system must be done against this backdrop with respect for all fundamental human rights. The collection of data to be used in the system and the storage of data can each independently implicate privacy rights and involve overlapping and…
Content Type: Report
Identity systems frequently rely on the collection and storage of biometric data during system registration, to be compared with biometric data collected at the point of a given transaction requiring identity system verification.
While courts have arguably overstated the effectiveness and necessity of biometric data for identity verification in the past, the frequency of biometric authentication failure is frequently overlooked. These failures have the potential to have profoundly…
Content Type: Report
National identity systems naturally implicate data protection issues, given the high volume of data necessary for the systems’ functioning.
This wide range and high volume of data implicates raises the following issues:
consent as individuals should be aware and approve of their data’s collection, storage, and use if the system is to function lawfully. Despite this, identity systems often lack necessary safeguards requiring consent and the mandatory nature of systems ignores consent…
Content Type: Report
While identity systems pose grave dangers to the right to privacy, based on the particularities of the design and implementation of the ID system, they can also impact upon other fundamental rights and freedoms upheld by other international human rights instruments including the International Covenant on Civil and Political Right and the International Covenant on Economic, Social and Cultural Rights such as the right to be free from unlawful discrimination, the right to liberty, the right to…
Content Type: Report
Rather than providing a list of arguments, as is the case in the other sections of this guide, the fifth section provides a general overview describing the absence of consideration of these themes in existing jurisprudence and the reasons why these themes warrant future consideration including identity systems’ implications for the rule of law, the role of international human rights law, and considerations of gender identity.
Democracy, the Rule of Law and Access to Justice: This analysis of…
Content Type: News & Analysis
New technologies continue to present great risks and opportunities for any users but for some communities the implications and harms can have severe consequences and one of the sectors facing increasing challenges to keep innovating whilst protecting themselves and the people they serve is the humanitarian sector.
Over the course of engagement with the humanitarian sector, one of our key observations has been how risk assessments undertaken in the sector omitted to integrate a hollistic…
Content Type: Video
You can listen and subscribe to the podcast where ever you normally find your podcasts:
Spotify
Apple podcasts
Google podcasts
Castbox
Overcast
Pocket Casts
Peertube
Youtube
Stitcher
And more...
Content Type: Long Read
Immunity Passports have become a much hyped tool to cope with this pandemic and the economic crisis. Essentially, with immunity passports those who are 'immune' to the virus would have some kind of certified document - whether physical or digital. This 'passport' would give them rights and privileges that other members of the community do not have.
This is yet another example of a crisis-response that depends on technology, as we saw with contact-tracing apps. And it is also yet another…
Content Type: Explainer
Definition
An immunity passport (also known as a 'risk-free certificate' or 'immunity certificate') is a credential given to a person who is assumed to be immune from COVID-19 and so protected against re-infection. This 'passport' would give them rights and privileges that other members of the community do not have such as to work or travel.
For Covid-19 this requires a process through which people are reliably tested for immunity and there is a secure process of issuing a document or other…
Content Type: Examples
Many of the steps suggested in a draft programme for China-style mass surveillance in the US are being promoted and implemented as part of the government’s response to the pandemic, perhaps due to the overlap of membership between the National Security Commission on Artificial Intelligence, the body that drafted the programme, and the advisory task forces charged with guiding the government’s plans to reopen the economy. The draft, obtained by EPIC in a FOIA request, is aimed at ensuring that…
Content Type: Video
You can find out more about Haki na Sheria here: http://hakinasheria.org/
Find out more about double registration in Keren's piece "In Kenya, thousands left in limbo without ID cards" in CodaStory: https://www.codastory.com/authoritarian-tech/kenya-biometrics-double-registration/
Find out more about the Huduma Namba case on our website: https://privacyinternational.org/news-analysis/3350/why-huduma-namba-ruling-matters-future-digital-id-and-not-just-kenya
You can listen and…
Content Type: Long Read
This week saw the release of a coronavirus tracking app within the United Kingdom, initially to be trialled in the Isle of Wight. Privacy International has been following this closely, along with other ‘track and trace’ apps like those seen in over 30 other countries.
The UK’s app is no different. It is a small part of a public health response to this pandemic. As with all the other apps, it is vital that it be integrated with a comprehensive healthcare response, prioritise people, and…
Content Type: News & Analysis
This week International Health Day was marked amidst a global pandemic which has impacted every region in the world. And it gives us a chance to reflect on how tech companies, governments, and international agencies are responding to Covid-19 through the use of data and tech.
All of them have been announcing measures to help contain or respond to the spread of the virus; but too many allow for unprecedented levels of data exploitation with unclear benefits, and raising so many red flags…
Content Type: Examples
The whistleblower said they were unable to find any legitimate reason for the high volume of the requests for location information. “There is no other explanation, no other technical reason to do this. Saudi Arabia is weaponising mobile technologies,” the whistleblower claimed.
The data leaked by the whistleblower was also seen by telecommunications and security experts, who confirmed they too believed it was indicative of a surveillance campaign by Saudi Arabia.
The data shows requests for…
Content Type: Examples
Bluetooth utilizes a device pairing mechanism based on elliptic-curve Diffie-Hellman (ECDH) key exchange to allow encrypted communication between devices. The ECDH key pair consists of a private and a public key, and the public keys are exchanged to produce a shared pairing key. The devices must also agree on the elliptic curve parameters being used. Previous work on the "Invalid Curve Attack" showed that the ECDH parameters are not always validated before being used in computing the resulted…
Content Type: Examples
“The BlueBorne attack vector requires no user interaction, is compatible to all software versions, and does not require any preconditions or configurations aside of the Bluetooth being active,” warned the researchers.
“Unlike the common misconception, Bluetooth enabled devices are constantly searching for incoming connections from any devices, and not only those they have been paired with,” they added.
“This means a Bluetooth connection can be established without pairing the devices at all.…
Content Type: Case Study
Having a right to a nationality isn’t predicated on giving up your right to privacy - and allowing whichever government runs that country to have as much information as they want. It is about having a fundamental right to government protection.
For the first time since 1951, Assam - a state in the north east of India - has been updating its national register of citizens (NRC), a list of everyone in Assam that the government considers to be an Indian citizen. The final version, published in…
Content Type: News & Analysis
Unlikely as it may seem, the UN institution that has one of the greatest potential to impact upon people’s rights around the world is now the UN Statistics Division. And why is that?
Last week, they had a crucial meeting where they endorsed the UN’s Legal Identity Agenda and the UN’s Legal Identity Task Force. The stakes could hardly be higher. One of the UN’s Sustainable Development Goals, SDG 16.9, states that “by 2030 provide legal identity for all including free birth…
Content Type: Long Read
Background
Kenya’s National Integrated Identity Management Scheme (NIIMS) is a biometric database of the Kenyan population, that will eventually be used to give every person in the country a unique “Huduma Namba” for accessing services. This system has the aim of being the “single point of truth”, a biometric population register of every citizen and resident in the country, that then links to multiple databases across government and, potentially, the private sector.
NIIMS was introduced…
Content Type: News & Analysis
On 30 January 2020, Kenya’s High Court handed down its judgment on the validity of the implementation of the National Integrated Identity Management System (NIIMS), known as the Huduma Namba. Privacy International submitted an expert witness testimony in the case. We await the final text of the judgment, but the summaries presented by the judges in Court outline the key findings of the Court. Whilst there is much there that is disappointing, the Court found that the implementation of NIIMS…