Advanced Search
Content Type: News & Analysis
This week, we read that a former Apple contractor who blew the whistle on the company’s programme to listen to users’ Siri recordings has decided to go public, in protest at the lack of action taken as a result of the July 2019 disclosures. The news adds to a series of revelations that have been reported over the past months.
While the issue raises serious questions regarding the compatibility of such practices with data protection laws, at the same time, it highlights a wider problem that…
Content Type: Case Study
You have the right to decent standards and dignity at work, and the right to join a union to protect yourself and your rights. That might come as a shock to Amazon - who have been using Covid-19 as a reason to undermine those rights.
Chris Smalls, an organiser and now former Amazon warehouse assistant manager, led a walkout at a New York City facility and within days he’d been fired under a dubious pretext.
The walkout was to ensure workers’ safety - they were asking for the warehouse to be…
Content Type: Explainer
In a scramble to track, and thereby stem the flow of, new cases of COVID-19, governments around the world are rushing to track the locations of their populace.
In this third installment of our Covid-19 tracking technology primers, we look at Satellite Navigation technology. In Part 1 of our mini-series on we discussed apps that use Bluetooth for proximity tracking. Telecommunications operators ('telcos'), which we discussed in Part 2, are also handing over customer data, showing the cell towers…
Content Type: Long Read
Today is 1st May, an international day of protest. It also marks a year since PI launched our new programme of work called ‘Defending Democracy and Dissent’.
One year on we find ourselves in a situation where 1 May protests in the streets will not be going ahead. Rights have been restricted around the world. Sadly we’re seeing some actors exploit this public health crisis to enhance their own power, expanding surveillance and opportunism.
Against this challenging back-drop we wanted to…
Content Type: Explainer
In a scramble to track, and thereby stem the flow of new cases of Covid-19, Governments around the world are rushing to track the locations of their populace. One way to do this is to leverage the metadata held by mobile service providers (telecommunications companies - "Telcos" - such as Hutchison 3 (Also known as Three), Telefonica (Also known as O2), Vodafone, and Orange) in order to track the movements of a population, as seen in Italy, Germany and Austria, and with the European Commission…
Content Type: Case Study
Over the past decade targeted advertisement has become exponentially more invasive. To enable targeted advertisement, massive amounts of data about individuals are collected, shared and processed often without their knowledge or consent. This information about us is then used to profile us and micro-target us to sell us products or influence our views.
This is a significant intrusion to our privacy inevitably affects our perogative not to reveal our thoughts; not to have our thoughts…
Content Type: Long Read
On 15th April Margaret Atwood, author of the Handmaid's Tale, gave an interview to BBC Radio 5 Live where she commented that ‘people may be making arrangements that aren’t too pleasant, but it’s not a deliberate totalitarianism’. You can read more about the interview in the Guardian.
While we agree with Margaret Atwood that we are not necessarily entering an era of "deliberate totalitarianism" we have written the following open letter (download link at the bottom of the page) to her as a ‘…
Content Type: Case Study
Since August 2017 742,000 Rohingya people - including children - fled across the Myanmar border to Bangladesh, escaping what the UN labelled a “textbook example of ethnic cleansing”.
In this context of ethnoreligious violence, Facebook has been a central figure. For many in Myanmar “Facebook is the internet” - as of January 2018 around 19 million people in Myanmar were facebook users, this is roughly equal to the number of internet users in the country.
A New York Times report revealed that…
Content Type: News & Analysis
This week International Health Day was marked amidst a global pandemic which has impacted every region in the world. And it gives us a chance to reflect on how tech companies, governments, and international agencies are responding to Covid-19 through the use of data and tech.
All of them have been announcing measures to help contain or respond to the spread of the virus; but too many allow for unprecedented levels of data exploitation with unclear benefits, and raising so many red flags…
Content Type: News & Analysis
Amid calls from international organisations and civil society urging for measures to protect the migrant populations in Greece and elsewhere, last week, the European Commission submitted a draft proposal to amend the general budget 2020 in order to, among other measures, provide assistance to Greece in the context of the COVID-19 outbreak.
Both at the Turkish-Greek border and in the camps on the Greek islands, there are severe concerns not only about the dire situation in which these people…
Content Type: Case Study
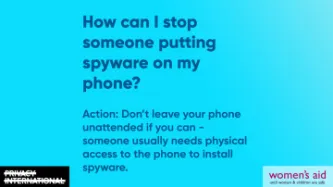
The right to privacy is crucial to protect a couple’s equal rights within marriage.
The recent rise of spyware as an “off-the-shelf” product that anyone can purchase has been extremely worrying, as installing spyware on someone else’s phone means getting access to their contacts, their messages, their google searches, their location and more - all without them knowing.
Spyware is, increasingly, becoming another way for abusive spouses to control and monitor their partners. Nearly a third of…
Content Type: Explainer
In a scramble to track, and thereby stem the flow of, new cases of Covid-19, Governments around the world are rushing to track the locations of their populace. One way to do this is to write a smartphone app which uses Bluetooth technology, and encourage (or mandate) that individuals download and use the app. We have seen such examples in Singapore and emerging plans in the UK.
Apps that use Bluetooth are just one way to track location. There are several different technologies in a smartphone…
Content Type: Case Study
In Peru, you get asked for your fingerprint and your ID constantly - when you’re getting a new phone line installed or depositing money in your bank account – and every Peruvian person has an ID card, and is included in the National Registry of Identity – a huge database designed to prove that everyone is who they say they are. After all, you can change your name, but not your fingerprint.
However, in 2019 the National Police of Peru uncovered a criminal operation that was doing just that:…
Content Type: News & Analysis
In the last few days, PI and its Network have been recording and documenting the measures being proposed by various governments, international institutions and companies to help contain the spread of Covid-19.
In a recent development, the Guardian have reported that the UK government is the latest to seek to use mobile phone location and other traffic data from telecommunication operators to help with measures the government may develop next as part of the response to Covid-19.
It comes…
Content Type: Case Study
There are 29.4 million refugees and asylum seekers across the globe today. These are people who have fled their countries due to conflict, violence or persecution seeking protection in safer environments.
People have protected those in need fleeing from dire situations since antiquity. However, over recent years, European countries have become increasingly hostile towards refugees - treating them as criminals instead of people in need.
In 2017, German authorities passed a…
Content Type: Case Study
The increasing deployment of highly intrusive technologies in public and private spaces such as facial recognition technologies (FRT) threaten to impair our freedom of movement. These systems track and monitor millions of people without any regulation or oversight.
Tens of thousands of people pass through the Kings Cross Estate in London every day. Since 2015, Argent - the group that runs the Kings Cross Estate - were using FRT to track all of those people.
Police authorities rushed in secret…
Content Type: News & Analysis
This piece was originally published by Unwanted Witness here.
Today marks exactly one year since Uganda passed its data protection law, becoming the first East African country to recognize privacy as a fundamental human right, as enshrined in Art 27 of the 1995 Uganda Constitution as well as in regional and International laws.
The Data Protection and Privacy Act, 2019 aims to protect individuals and their personal data by regulating processing of personal information by state and non-state…
Content Type: Case Study
In 2015, a man in Connecticut was charged with murdering his wife based on evidence from her Fitbit. Richard Dabate, the accused, told the police that a masked assailant came into the couple’s suburban home at around 9am on 23 December 2015, overpowering Dabate then shooting his wife as she returned through the garage.
However, the victim’s fitness tracker told a different story. According to data from the device, which uses a digital pedometer to track the wearer’s steps, Dabate’s wife was…
Content Type: Long Read
This piece was written by Aayush Rathi and Ambika Tandon, who are policy officers at the Centre for Internet and Society (CIS) in India. The piece was originally published on the website Economic Policy Weekly India here.
In order to bring out certain conceptual and procedural problems with health monitoring in the Indian context, this article posits health monitoring as surveillance and not merely as a “data problem.” Casting a critical feminist lens, the historicity of surveillance practices…
Content Type: Examples
Recent study shows that Americans are wary of data from smart speakers being used in criminal investigations, the Pew Research Center reported. A recent study showed that 49% of Americans answered that it is unacceptable for smart speakers companies to share audio recordings of their customers with law enforcement in order to help with criminal investigations. Only 25% said it is acceptable. Aparently, this result contrasts with some other data use practices measured in the same survey. For…
Content Type: Long Read
We are excited to spotlight our Reproductive Rights and Privacy Project!
The Project is focused on researching and exposing organisations that collect and exploit the information of those seeking to exercise their reproductive rights. Working together with PI partners, other international grassroots organisations and NGOs, PI is researching and advocating against this data exploitation.
So, what are reproductive rights?
Sexual and reproductive rights, which are contained within Economic,…
Content Type: News & Analysis
In the last few months strong concerns have been raised in the UK about how police use of mobile phone extraction dissuades rape survivors from handing over their devices: according to a Cabinet Office report leaked to the Guardian, almost half of rape victims are dropping out of investigations even when a suspect has been identified. The length of time it takes to conduct extractions (with victims paying bills whilst the phone is with the police) and the volume of data obtained by the…
Content Type: Examples
A woman was killed by a spear to the chest at her home in Hallandale Beache, Florida, north of Miami, in July. Witness "Alexa" has been called yet another time to give evidence and solve the mystery. The police is hoping that the smart assistance Amazon Echo, known as Alexa, was accidentally activated and recorded key moments of the murder. “It is believed that evidence of crimes, audio recordings capturing the attack on victim Silvia Crespo that occurred in the main bedroom … may be found on…
Content Type: Long Read
The pressing need to fix our cybersecurity (mis)understandings
Despite all the efforts made so far by different, cybersecurity remains a disputed concept. Some states are still approving cybersecurity laws as an excuse to increase their surveillance powers. Despite cybersecurity and cybercrime being different concepts, the confusion between them and the broad application of criminal statutes is still leading to the criminalise legitimate behaviour.
All of this represents a sizable challenge…
Content Type: Long Read
In this piece we examine mobile phone extraction, relying on publicly available information and Privacy International’s experience from conducting mobile phone extraction using a Cellebrite UFED Touch 2. We welcome input from experts in the field. This is a rapidly developing area. Just as new security features are announced for phones, so too new methods to extract data are found.
[All references can be found in the pdf version below.]
General explanation of mobile phone…
Content Type: News & Analysis
Photo by Daniel Jensen on Unsplash
Everyone is talking about Facebook's end-to-end encryption plans and the US, UK and Australian government's response. Feeling lost? Here is what you need to know.
What's Facebook trying to do?
First let's be clear: Facebook has many faults when it comes to privacy. It's also suffered a number of security failures recently. See here for instance.
In response to their successive failures to protect your privacy, Facebook announced in their 'pivot to privacy…
Content Type: News & Analysis
Today’s announcement regarding the UK and US agreement signed pursuant to the US CLOUD Act is being touted on both sides of the Atlantic as a major victory for law enforcement and security. But it is a step backward for privacy.
And it’s far more complicated than their press release and letter to industry.
The agreement replaces the prior system, under which law enforcement agencies from around the world, including the UK, had to meet US legal standards in order to get access to content held…
Content Type: Long Read
In December 2018, Privacy international exposed the dubious practices of some of the most popular apps in the world.
Out of the 36 apps we tested, we found that 61% automatically transfer data to Facebook the moment a user opens the app. This happens whether the user has a Facebook account or not, and whether they are logged into Facebook or not. We also found that some of those apps routinely send Facebook incredibly detailed and sometimes sensitive personal data. Again, it didn’t matter if…
Content Type: Long Read
Image credit: Emil Sjöblom [ShareAlike 2.0 Generic (CC BY-SA 2.0)]
Prepaid SIM card use and mandatory SIM card registration laws are especially widespread in countries in Africa: these two factors can allow for a more pervasive system of mass surveillance of people who can access prepaid SIM cards, as well as exclusion from important civic spaces, social networks, and education and health care for people who cannot.
Mandatory SIM card registration laws require that people provide personal…
Content Type: Video
Watch our video primer (1m54s) on how political advertisers use highly detailed data about you to target political adverts at you.
Read about some simple steps you can take to minimise the amount of political ads you see online and questions you can be asking of those that profit from your data.