Search
Content type: Examples
Even after they move out, domestic abusers may retain control over their former residence via Internet of Things devices and the mobile phone apps that control them. Using those tools, abusers can confuse, intimidate, and spy upon their former spouses and partners. Lack of knowledge about how these technologies work means that those who complain are often not taken seriously. Even the victims themselves may believe it's all in their minds; lawyers are struggling to develop language to add to…
Content type: Examples
In 2017, a website run by the Jharkhand Directorate of Social Security leaked the personal details of over.1 million Aadhaar subscribers, most of them old age pensioners who had enabled automatic benefits payment into their bank accounts. Aadhaar is a 12-digit unique identification number issued to all Indian residents based on their biometric and demographic data. Both cyber security agencies and the Supreme Court have expressed concerns over its security,…
Content type: News & Analysis
There are three good reasons why security is so hard for NGOs. First, we are afraid to speak about meaningful security. Second, we focus on the wrong areas of security and in turn spend money and prioritise the wrong things. Third, we struggle to separate the world we want from the worlds we build within our own organisations. At PI we have failed and struggled with each of these for over 20 years. Out of exhaustion, we decided to do something about it: we are building an open framework, a…
Content type: News & Analysis
This is the story of Privacy International's journey to building more secure services. Data collection and administering sensitive data on the open web is risky, and PI had to learn this the hard way.
Many companies say that the privacy of their audiences is their top priority. But do they mean it? Do they invest in it? Doing security on tight budgets is incredibly hard. But it is the natural state of the non-profit sector. We learned this through challenging experiences.…
Content type: Advocacy
Thornsec is a piece of software developed by Privacy International’s Tech Team which is an automated way to deploy, test, and audit internal and external services for an organisation, saving a lot of time and creating a sustainable security model. We are using this software to run all of Privacy International’s services – website, calendar, project management tools, Tor hidden services, VPNs. The whole system runs on two servers and the whole cost is around US$1000 to set up.
Thornsec is…
Content type: Report
In this paper, Privacy International explores* what it means to be secure, and how governments and companies enact policies and laws that undermine security globally. Good cyber security policies and practices put people and their rights at the centre. By prioritising the individual and protecting people, devices and networks, governments could take advantage of a real opportunity - to give something technically complex a human element. In short, giving the tin man a heart.
*This…
Content type: News & Analysis
Photo Credit: MoD UK
‘Security’ in the policy world has practically no currency without a specific prefix. For example, we could discuss 'national' security as distinct from 'consumer' security or 'energy' security. ‘Cyber’ security is the new prefix on the policy block, and it is gradually forcing a rethink on what it means to be secure in a modern society. In the course of Privacy International’s work globally, we have observed that many governments frame cyber security as national security…
Content type: News & Analysis
The past few years have seen a huge rise in the number of attacks both active and passive, against organisations big and small. Attacks against organisations happen for a multitude of reasons: extortion via "ransomware", exfiltration of commercial secrets, or just "the lulz". While this can be crippling to a commercial business, it can potentially be devastating to an NGO, especially those which work to hold powerful institutions to account. The types of information held by such NGOs could…
Content type: News & Analysis
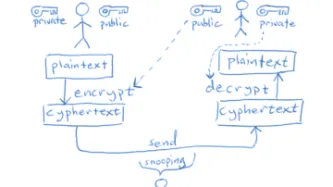
Dear Politicians,
With elections coming up and quite a few cringe-worthy comments that have come from many of you and from all sides of the political spectrum, we figured it was time to have a chat about encryption.
First, let’s say what you shouldn’t do:
call for boycotts of companies because they protect their users’ data even from the companies themselves.
say something like “we’ll develop a Manhattan-level project on this” (which, as we’ll remind you, ended up with the creation of a…
Content type: News & Analysis
On a hot day in Nairobi, our researcher is speaking to an officer of Kenya’s National Intelligence Service (NIS). The afternoon is wearing on and the conversation has turned to the presidential elections, taking place in August this year. He has just finished describing the NIS’ highly secret surveillance powers and the disturbing ways in which these powers are deployed.
“It is what you might call ‘acceptable deaths,’” he states about the misuse of communications surveillance powers. “People…
Content type: News & Analysis
This guest piece was written by Elonnai Hickok and Vipul Kharbanda of the Centre for Internet and Society. It does not necessarily reflect the views or position of Privacy International.
In light of the complex challenges and threats posed to, and by, the field of information telecommunications in cyberspace, in 1998 the draft resolution in the First Committee of the UN General Assembly was introduced and adopted without a vote (A/RES/53/70)…
Content type: News & Analysis
The connectivity afforded by the internet has changed the world forever. While the increasing ‘corporatization’ of what many still feel is an open, non-hierarchical, largely uncensored and unfiltered ecosystem, this is increasingly not the case. The emergence of the ‘Internet of Things’ will soon throw into sharp relief who owns the internet and who owns the data we all generate when using the internet. Companies today have a vested interest in portraying their products as safe and…
Content type: News & Analysis
Privacy can be seen as a reflex of innovation. One of the seminal pieces on the right to privacy as the 'right to be let alone emerged in response to the camera and its use by the tabloid media. Seminal jurisprudence is in response to new surveillance innovations... though often with significant delays.
While one approach would be to say that privacy is a norm and that with modern technologies the norm must be reconsidered and if necessary, abandoned; I think there’s an interesting idea around…
Content type: News & Analysis
Everyone wants to know what you need to do to be i) happy, ii) fit, iii) secure. And the easier and more listy it is, the better.
The Guardian recently published an article that left PI’s techies sceptical, to say the least. “Extreme online security measures to protect your digital privacy – a guide” offered nine pieces of advice to stay secure online, including covering your house with a few layers of aluminium (!!!).
While there is no one-solution-fits-all when it comes to security and…
Content type: News & Analysis
The much maligned Prevention of Electronic Crimes Bill (PECB) was dealt a critical blow by senior Senate members on Tuesday in Pakistan. Digital Rights Foundation, in conjunction with Bolo Bhi, held a consultation for members of the Pakistan Senate, other lawmakers, members of civil society, and the media.
The aim of the consultation was to discuss the Bill, the problematic provisions and amendments that have been suggested in its most recent version, and the steps…
Content type: News & Analysis
The National Privacy Commission has had to firefight a huge leak of voter data in Philippines just one month before the elections
Raymund Liboro, the Philippines’ National Privacy Commissioner, has had a tough few weeks. Barely has his office even existed -- he was appointed in March -- than it is having to firefight what is being reported as the country’s most massive data breach to date. On 27 March, a hacker broke in to the national Commission on Elections (Comelec)’s…
Content type: Long Read
Written by: Maria del Pilar Saenz
With a raft of recent scandals involving proven and possible abuses of surveillance systems by state institutions, there is a clear need to generate policy and practice in Colombia that promotes respect for human rights. It is necessary to keep this in mind as an emerging public policy discussion on cybersecurity led by CONPES (The National Council for Economic and Social Policy) begins in Colombia. This series of reforms will serve as the policy basis…
Content type: News & Analysis
This guest post was written by Nighat Dad and Adnan Chaudhry of Digital Rights Foundation.
It is the role of the state to protect its citizens from threats to their life and liberty. But in protecting its citizens, the state’s own aims cannot be counterproductive and erode the security found in rights like privacy and freedom of expression that are vital to a democratic system.
However, it has too often been the case that governments will pursue and enact legislation that provides more…
Content type: News & Analysis
While two of the Vice journalists who were recently arrested in Turkey and charged with terror offenses have now been released, this remain a deeply concerning incident.* It is the latest episode in what is a pincer movement against our right to protect our data.
Two British journalists and their Turkey-based Iraqi translator working for VICE News were arrested last Thursday and charged with "engaging in terrorist activity". According to Turkish authorities, one member of the group had an…
Content type: News & Analysis
FREAK, the latest security vulnerability to be exposed that has implications for millions of supposedly secure websites, is just the most recent example of something privacy and security advocates have been saying for some time: when governments meddle with our security technologies, it hurts us all.
When the State advocates for backdoors into our communications, they cannot secure them properly and malicious actors can get in. When our elected officials pontificate about spying on us to…
Content type: News & Analysis
In the wake of tragic attacks in France, politicians from across the world are calling for dramatically expanded surveillance powers, to spy on our phonecalls, ban encrypted communications such as WhatsApp and iMessage, and store details about our international travels for years on end.
If it feels like you've heard this story before, it's because you have. With each violent attempt by extremists to terrorise society, our political leaders dust off old, failed proposals such as the UK…
Content type: News & Analysis
Just a few weeks ago, thousands of Argentinians had their privacy rights violated when the country’s electoral registration roll, which had been made available online, experienced a major leak of personal data following the presidential election.
Despite some early warnings on the weaknesses of the system, the government did nothing to fix the situation, allowing serious technical flaws in an online system to persist and refusing to respond to the crisis, further…
Content type: News & Analysis
Privacy International welcomes the absence of a Communications Data Bill in the Queen's Speech. The Communications Data bill was originally set to significantly expand the powers of communications surveillance in the UK and set another bad standard globally. Because of the work by Parliamentarians, a concerted effort by civil society groups and some within industry, this expansion was avoided, for now. However the Queen's Speech did include a mention of new proposals:
In relation…
Content type: News & Analysis
Anonymous proxy service HideMyAss.com - "a leading online privacy website" according to its own homepage - today admitted handing over user logs to law enforcement agencies.
We commend companies running privacy-protecting services. We need more like them. But we also need them to keep their word. Their website claims "Our free web proxy is a secure service that allows you to surf anonymously online in complete privacy" and their pro paid-for version promises that users can "…
Content type: News & Analysis
The Home Office has been planning a grab for new communications surveillance powers since 2006; today, the Draft Communications Data Bill established in legislative language their ambitions.
Yes, as they will point out, it isn't their the full scope of their ambitions. In 2008, under Labour, they proposed the idea of a vast centralised database of the nation's communications data. In 2009 they abandoned the idea of a central database. Since then, a new government has been elected,…
Content type: News & Analysis
Other human rights organisations often ask us what they should to when it comes to their infosec needs. Should they run their own mail server, or trust Gmail? Should they merge their calendars by email (!), a local server, or use some cloud solution?
We honestly don't know what to tell them. In fact, we are unsure of what we ourselves should be doing. We know that there are risks of keeping things local (e.g. lack of redundancy), and there are risks of data being stored…
Content type: News & Analysis
Privacy International has briefed the UK House of Commons Treasury subcommittee on the risks to UK census data if a company with a US data centre is called on to run the census. Under weak US laws on safeguarding personal information, the UK census data could be abused without any knowledge of the UK government.
We filed a letter with the subcommittee to respond to the government minister's claims to the Commons that the government had no concerns about the US government gaining access to the…