Advanced Search
Content Type: Explainer
What is social media monitoring?
Social media monitoring refers to the monitoring, gathering and analysis of information shared on social media platforms, such as Facebook, Twitter, Instagram and Reddit.
It may include snooping on content posted to public or private groups or pages. It may also involve “scraping” – grabbing all the data from a social media platform, including content you post and data about your behaviour (such as what you like and share).
Through scraping and other tools…
Content Type: Explainer
What are my 'unique identifiers' and where are they stored?
Your phone and your SIM card contain unique identifiers about you, which can be accessed by the police to identify you.
The IMSI (International Mobile Subscriber Identity) is a unique number associated with your SIM card. It doesn't change, even if you put the SIM card into a different phone.
If you have a mobile phone subscription, the IMSI will be associated with personal information such as your name and address.
The IMEI (…
Content Type: Explainer
Where are my communications stored?
Text messages/phone calls: Traditional cellphone communications happen over the cellular network. You usually access those with the text message and phone call apps that are provided as standard on your phone. While phone calls aren’t stored anywhere, text messages are stored locally on your and the recipient’s devices. They might also be temporarily stored by the network provider.
Messaging apps: Messaging platforms enable fairly secure communication…
Content Type: Explainer
Where is my phone's location data stored?
Your phone can be located in two main ways, using GPS or mobile network location:
1. GPS
GPS (that stands for Global Positioning System) uses satellite navigation to locate your phone fairly precisely (within a few metres), and relies on a GPS chip inside your handset.
Depending on the phone you use, your GPS location data might be stored locally and/or on a cloud service like Google Cloud or iCloud. It might also be collected by any app that you…
Content Type: Explainer
What is predictive policing?
Predictive policing programs are used by the police to estimate where and when crimes are likely to be committed – or who is likely to commit them. These programs work by feeding historic policing data through computer algorithms.
For example, a program might evaluate data about past crimes to predict where future crimes will happen – identifying ‘hot spots’ or ‘boxes’ on a map. But the data these programs use can be incomplete or biased, leading to a ‘feedback…
Content Type: Explainer
What is LEDS?
LEDS is a new mega-database currently being developed by the UK Home Office.
LEDS will replace and combine the existing Police National Database (PND) and the Police National Computer (PNC). The aim is to provide police and others with a super-database, with on-demand, at the point of need access, containing up-to-date and linked information about individuals’ lives.
Once your details are in LEDS, numerous agencies will have access to that information (e.g. HMRC and DVLA),…
Content Type: Explainer
What are police drones?
Drones are remotely controlled Unmanned Aerial Vehicles (UAVs) of varying sizes.
They usually come equipped with cameras and might be enabled with Facial Recognition Technology.
Drones can be equipped with speakers, surveillance equipment, radar and communications interception tools, such as ‘IMSI catchers’.
How might drones be used during protests?
Camera-enabled drones may be used to remotely monitor and track people’s movements in public spaces, including at…
Content Type: Explainer
What do Body Worn Video cameras do?
Body worn video (BWV) cameras can be attached to a police officer’s clothing – often at chest, shoulder or head level – and record video, including sound, from the officer’s perspective.
BWV cameras will probably be visible to you, and when it’s recording, a flashing light should appear on the device.
How might body worn video cameras be used at a protest?
BWV cameras may be used at protests to monitor actions of protestors.
They do not usually…
Content Type: Explainer
What is gait recognition technology?
Gait recognition technology (GRT) can analyse the shape of an individual’s body and the unique way in which that body moves when walking or running, which can then be used to identify them.
GRT works in a similar way to facial recognition technology. But the two main differences are:
GRT may be used at a fairly long range (at the time of writing, about 165 feet / 50 metres), unlike FRT which generally requires more close up, detailed facial images…
Content Type: Explainer
What is Facial Recognition Technology?Facial recognition technology (FRT) collects and processes data about people’s faces, and can be used to identify people. FRT matches captured images with images stored in existing databases or ‘watchlists’.How might it be used in relation to a protest?FRT may be used to monitor, track and identify people’s faces in public spaces, including at protests. This may be done openly or surreptitiously, without people knowing or consenting.FRT-enabled cameras can…
Content Type: Explainer
What is hacking?
Hacking refers to finding vulnerabilities in electronic systems, either to report and repair them, or to exploit them.
Hacking can help to identify and fix security flaws in devices, networks and services that millions of people may use. But it can also be used to access our devices, collect information about us, and manipulate us and our devices in other ways.
Hacking comprises a range of ever-evolving techniques. It can be done remotely, but it can also include physical…
Content Type: Explainer
What is an IMSI catcher?
‘IMSI’ stands for ‘international mobile subscriber identity’, a number unique to your SIM card. IMSI catchers are also known as ‘Stingrays’.
An ‘IMSI catcher’ is a device that locates and then tracks all mobile phones that are connected to a phone network in its vicinity, by ‘catching’ the unique IMSI number.
It does this by pretending to be a mobile phone tower, tricking mobile phones nearby to connect to it, enabling it to then intercept the data from that phone…
Content Type: Explainer
What are ‘cloud extraction tools’ and what do they do?
Cloud extraction technology enables the police to access data stored in your ‘Cloud’ via your mobile phone or other devices.
The use of cloud extraction tools means the police can access data that you store online. Examples of apps that store data in the Cloud include Slack, Instagram, Telegram, Twitter, Facebook and Uber.
How might cloud extraction tools be used at a protest?
In order to extract your cloud data, the police would…
Content Type: Long Read
In May 2019, the UK Department for Work and Pensions (DWP) – the department in charge of welfare – published their two-part staff guide on conducting fraud investigations. Privacy International went through the 995 pages to understand how those investigations happen and how the DWP is surveilling benefits claimants suspected of fraud.
Anyone who has flipped through a tabloid will have seen articles exposing the so-called “benefits-cheats,” people who allegedly trick the benefits systems for…
Content Type: Long Read
Back in 2019, we read through a 1000-page manual released by the UK Department for Work and Pensions (DWP) describing how they conduct investigations into alleged benefits fraud. While out in the open and accessible to anyone, the guide turned out to be a dizzying dive into a world where civil servants are asked to stand outside someone’s door to decide if they are indeed single or disabled and have to be reminded that living together as a married couple is not an offense. The guide – which…
Content Type: News & Analysis
Earlier this week, the UK Government announced that no immigration status checks will be carried out for migrants trying to register with their GP and get vaccinated. But temporary offers of safety are not enough to undo the decades of harm caused by policies that have embedded immigration controls into public services.
Years of charging migrants for healthcare and sharing patient data with the Home Office has eroded trust between migrant communities and the NHS. As a result, they might not…
Content Type: Advocacy
This letter is also available in Spanish.
Dear Mr. Zuckerberg and Mr. Pichai,
In the past few years, you have pioneered important transparency tools to help your platform users understand, learn about and contextualise the political advertising they see. We agree that advertiser verification processes and ad repositories are key safeguards against online manipulation and misinformation. However, we are saddened to observe that these benefits have not been equally distributed among your global…
Content Type: Long Read
Among the many challenges of 2020, the impact on elections around the world kept us all on the edge of our seats. 75 countries postponed national and local elections due to Covid 19. Of the elections that went ahead, we saw Covid safe measures at polling stations (South Korea led the way forward in April) an increase in postal voting (who can forget the USA, but also Poland) and political parties in Uganda conducting "virtual" campaigns as mass rallies and in person campaign meetings were…
Content Type: Long Read
Political parties depend on data to drive their campaigns, from deciding where to hold rallies, which campaign messages to focus on in which area, and how to target supporters, undecided voters and non-supporters, including with ads on social media. Political parties increasingly hire private companies to do the bulk of this work, and our primary concern is how these companies use personal data to “profile” people and drive election campaigning.
As part of PI’s programme of work on Defending…
Content Type: Long Read
As we see Covid-19 vaccination programmes beginning around the world, for the first time since the start of the pandemic there seems to be a light at the end of the tunnel as the fruition of truly unrivalled global scientific efforts has given us hope of saving lives, reopening our societies, and going back to “normal”.
This great moment of hope must not be seen opportunistically as yet another data grab. The deployment of vaccines, and in particular any “immunity passport” or certificate…
Content Type: Advocacy
Section 187 of the Data Protection Act read with Article 80 of the GDPR gives individuals the option to seek assistance from public interest non-profit organisations to take action against data controllers which have infringed their data rights. In this role, non-profit organisations may:
make complaints to the regulator on the individual’s behalf;
represent the individual in the courts when seeking a resolution of those complaints; and
bring legal claims against organisations they believe…
Content Type: News & Analysis
An excerpt of this piece was first published in June 2020 in Adbusters, an international not-for-profit magazine produced by a global collective of artists and activists who want to 'shake up complacent consumer culture'.
Big oil. Big tobacco. Big pharma. How did we let ‘big tech’ happen? You would have thought humanity would learn its lesson. That nothing good comes of the mass accumulation and concentration of power into the hands of so few.
The internet was meant to be different. No…
Content Type: Advocacy
International data transfers are an important feature of the present-day global economy. However, when crossing borders, data should also be accompanied by strong and effective privacy and personal data protections. Laws, such as the General Data Protection Regulation (GDPR), play an important role in ensuring data flows respect with privacy.
Trade negotiations that cover cross-border data flows can complicate this. All 80 countries that are part of digital trade negotiations should be able to…
Content Type: News & Analysis
Le « Fonds fiduciaire d’urgence de l’Union européenne en faveur de la stabilité et de la lutte contre les causes profondes de la migration irrégulière et du phénomène des personnes déplacées en Afrique » (le « fonds fiduciaire pour l’Afrique ») ne fait pas les grands titres (et il est plutôt difficile à retenir), mais son influence est vaste et aura des conséquences pendant plusieurs décennies sur la vie de millions de personnes sur le continent africain.
Mis en place suite à la « crise…
Content Type: News & Analysis
The “EU Trust Fund for Stability and Addressing Root Causes of Irregular Migration and Displaced Persons in Africa” (EUTF for Africa) isn’t exactly headline news (and nor does it exactly roll off the tongue), but its influence is vast and will be felt for decades to come for millions of people across Africa.
Set up in the wake of the 2015 ‘migration crisis’ in Europe and largely made up of money earmarked for development aid (80% of its budget comes from development and humanitarian aid funds…
Content Type: Video
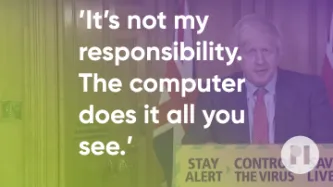
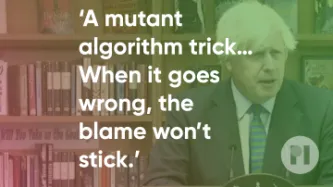
The two-minute video splices together clips of UK Prime Minister Boris Johnson, cleverly editing his speeches so that he mouths sentences such as:
'Coronavirus won’t affect you if your immunity passport’s blue'
'You can tell our technology’s going well, we’re running this whole thing in Excel'
'A mutant algorithm trick, when it goes wrong, the blame won’t stick'
'Our system’s world-beating at self-defeating'
'So when results are not forthcoming, don’t ask me, ask Dominic…
Content Type: Press release
The new satirical video is a critique of the government's reliance on 'technological solutionism' in the fight against Coronavirus and increasingly across public services more widely, and their willingness to then scapegoat ‘mutant algorithms’ when their hopes for technological panaceas inevitably fail.
The two-minute video splices together clips of Prime Minister Boris Johnson, cleverly editing his speeches so that he mouths sentences such as:
'Coronavirus won’t affect you if your immunity…
Content Type: Long Read
An edited version of this article was originally published on the EDRi website in September 2020.
Introduction
Monopolies, mergers and acquisitions, anti-trust laws. These may seem like tangential or irrelevant issues for privacy and digital rights organisations. But having run our first public petition opposing a big tech merger, we wanted to set out why we think this is an important frontier for people's rights across Europe and indeed across the world.
In June, Google notified the…
Content Type: News & Analysis
The Law Enforcement Data Service (LEDS) is a unified, common interface to a new mega-database currently being developed by the Home Office National Law Enforcement Data Programme (NLEDP). We believe that the development of the programme poses a threat to privacy and other rights and must be subjected to strong oversight, safeguards, and transparency measures.
As we explained in our analysis, the data in LEDS is vast, ever-increasing, worryingly mixes both evidential and intelligence material –…
Content Type: News & Analysis
Back in January, Privacy International and over 50 other organisations wrote to Google asking the company to take action over pre-installed apps that cannot be deleted (often known as “bloatware”), which can leave users vulnerable to their data being collected, shared and exposed without their knowledge or consent. Thousands of people from over 50 countries signed our petition supporting this ask. We welcome the constructive conversations we had with Google following this campaign and for the…