Advanced Search
Content Type: News & Analysis
Amid calls from international organisations and civil society urging for measures to protect the migrant populations in Greece and elsewhere, last week, the European Commission submitted a draft proposal to amend the general budget 2020 in order to, among other measures, provide assistance to Greece in the context of the COVID-19 outbreak.
Both at the Turkish-Greek border and in the camps on the Greek islands, there are severe concerns not only about the dire situation in which these people…
Content Type: Long Read
Commercial interests seem to often overshadow the EU’s stance as a global privacy leader. After looking at Europes's shady funds to border forces in the Sahel area, Niger's new biometric voting system, and attempts to dismantle smugglers networks powered by Europe's gifts of surveillance, freelance journalist Giacomo Zandonini looks at the battle for data protection and digital rights in the continent.
What do a teenage labourer on a marijuana farm in Lesotho, a…
Content Type: Long Read
It was a quiet evening in Agadez, a bustling Saharan city in the centre of Niger. Thirty-five year old Agali Ahmed was sipping tea at a friend’s place, as he often did, when he received a message: police were at his uncle’s house. When he got there, Ahmed saw men in plainclothes, standing around the building’s gate. Inside, more men were searching the apartment. Three white men, who Ahmed guessed were Spanish, asked for his phone and started taking pictures of him. They told him to follow them…
Content Type: Long Read
The European Union (EU) spends billions on research and development aimed at driving economic growth and jobs, as well as furthering the bloc’s broader agenda. Within the current budget, known as Horizon 2020 and covering the years 2014-2020, some €80 billion has been made available for research in a huge number of areas, ranging from finding cures for diseases to helping keep the earth viable for life.
From the same budget, it also funds a lot of projects aimed at developing surveillance…
Content Type: Case Study
On 3 December 2015, four masked men in plainclothes arrested Isnina Musa Sheikh in broad daylight (at around 1 p.m.) as she served customers at her food kiosk in Mandera town, in the North East of Kenya, Human Rights Watch reported. The men didn’t identify themselves but they were carrying pistols and M16 assault rifles, commonly used by Kenyan defence forces and the cars that took her away had their insignia on the doors. Isnina’s body was discovered three days later in a shallow grave about…
Content Type: Case Study
The prohibition against torture is absolute. There are no exceptional circumstances whatsoever which can be used to justify torture.
And yet, torture is still being carried out by state officials around the world, driven by states’ ability to surveil dissidents, and intercept their communications.
In 2007, French technology firm Amesys (a subsidiary of Bull) supplied sophisticated communications surveillance systems to the Libyan intelligence services. The systems allegedly permitted the…
Content Type: Long Read
Sitting on the ground inside an unadorned courtyard in Koira Tegui, one of Niamey’s most popular districts, Halimatou Hamadou shows a copy of what, she’s been told, is a certificate of birth.
The 33 year old woman, who’s unable to read and write, received it days earlier during a crowded public ceremony at a nearby primary school.
“It’s my first document ever,'' she says, with surprise.
Thanks to the paper, she’ll be able to take part in a crucial passage for the future of Niger: the…
Content Type: Advocacy
Earlier this year, the UN Special Rapporteur on freedom of expression called for an “immediate moratorium on the global sale and transfer of private surveillance technology”, warning that “unlawful surveillance continues without evident constraint”, is leading to arbitrary detention, torture and possibly to extrajudicial killings.
Without urgent action, there is every reason to believe that the situation will only get worse for people around the world.
At Privacy…
Content Type: Report
In September 2019, Privacy International filed 10 access to documents requests to EU bodies regarding the transfer of surveillance capabilities to non-EU countries. The requests seek documents providing information on the transfer of personal data, surveillance technology, training, financing, and legislation to non-EU countries. The requests were submitted to:
Frontex
Europol
The European Union Agency for Law Enforcement Training
The Directorate-General for Economic and…
Content Type: News & Analysis
Photo: The European Union
“Border Externalisation”, the transfer of border controls to foreign countries, has in the last few years become the main instrument through which the European Union seeks to stop migratory flows to Europe. Similar to the strategy being implemented under Trump’s administration, it relies on utilising modern technology, training, and equipping authorities in third countries to export the border far beyond its shores.
It is enabled by the adoption…
Content Type: News & Analysis
Photo by Francesco Bellina
The wars on terror and migration have seen international funders sponsoring numerous border control missions across the Sahel region of Africa. Many of these rely on funds supposed to be reserved for development aid and lack vital transparency safeguards. In the first of a series, freelance journalist Giacomo Zandonini sets the scene from Niger.
Surrounded by a straw-yellow stretch of sand, the immense base of the border control mobile company of Maradi, in southern…
Content Type: Long Read
Photo: Francesco Bellina
Driven by the need to never again allow organised mass murder of the type inflicted during the Second World War, the European Union has brought its citizens unprecedented levels of peace underpinned by fundamental rights and freedoms.
It plays an instrumental role in protecting people’s privacy around the world; its data protection regulation sets the bar globally, while its courts have been at the forefront of challenges to unlawful government surveillance…
Content Type: Advocacy
Agreed in 2015, the EU Trust Fund for Africa uses development aid and cooperation funds to manage and deter migration to Europe. It currently funds numerous projects presenting urgent threats to privacy, including developing biometric databases, training security units in surveillance, and equipping them with surveillance equipment. There has been no decision made about the future of the Fund pending the outcome of negotiations on the EU's next budget.
This paper…
Content Type: Advocacy
The Neighbourhood, Development and International Cooperation Instrument (NDICI) is a external instrument proposed under the EU's next 2021-2027 budget. It will provide funding for surveillance, border security, and migration management projects in third countries currently undertaken by a number of projects across various funds which are to form part of the NDICI. Several raise significant concerns regarding the right to privacy.
This paper summarises the NDICI and provides a…
Content Type: Advocacy
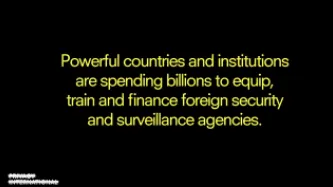
This report, which was authored by Lorand Laskai, who is a JD Candidate at Yale Law School, provides an overview of the surveillance technology and training that the Chinese government supplies to countries around the world. China, European countries, Israel, the US, and Russia, are all major providers of such surveillance worldwide, as are multilateral organisations such as the European Union. Countries with the largest defence and security sectors are transferring technology and…
Content Type: News & Analysis
Photo: The European Union
On 2 September 2019, Privacy International, together with 60 other organisations, signed an open letter to the European Parliament to express our deep concern about upcoming EU policy proposals which undermine the EU’s founding values of human rights, peace and disarmament.
Since 2017, the EU has diverted funds towards security research and security capacity-building in countries around the world. The proposal for the EU's next budget (2021-2027) will…
Content Type: News & Analysis
Foto: US AID
El presidente estadounidense Trump ha estado recortando la ayuda a Centroamérica, incluyendo un recorte sorpresivo de aproximadamente 500 millones de dólares a los países del “Triángulo del Norte” (El Salvador, Guatemala y Honduras), al parecer como castigo por “no haber hecho absolutamente nada” para impedir la emigración hacia los Estados Unidos.
Los fondos restantes están siendo reorientados,en su gran mayoría y deliberadamente, al gasto para…
Content Type: News & Analysis
Picture Credit: US AID
US President Trump has been cutting aid to Central America, including a surprise cut of approximately $500m in aid to the “Northern Triangle” countries of El Salvador, Guatemala, and Honduras, apparently as punishment for “doing absolutely nothing” to prevent emigration to the US.
What remains of the funds is largely and deliberately being repurposed for spending on the US’s own security interests: indeed, one area which his…
Content Type: Long Read
Photo By: Cpl. Joel Abshier
‘Biometrics’ describes the physiological and behavioural characteristics of individuals. This could be fingerprints, voice, face, retina and iris patterns, hand geometry, gait or DNA profiles. Because biometric data is particularly sensitive and revealing of individual’s characteristics and identity, it can be applied in a massive number of ways – and has the potential to be gravely abused.
Identification systems across the world increasingly rely on…
Content Type: Long Read
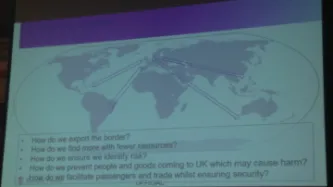
The UK border authority is using money ring-fenced for aid to train, finance, and provide equipment to foreign border control agencies in a bid to “export the border” to countries around the world.
Under the UK Border Force’s “Project Hunter”, the agency works with foreign security authorities to bolster their “border intelligence and targeting” capabilities with UK know-how and equipment.
As well as the provision of equipment and training, the Border Force is also advising countries on…
Content Type: Long Read
Cellebrite, a surveillance firm marketing itself as the “global leader in digital intelligence”, is marketing its digital extraction devices at a new target: authorities interrogating people seeking asylum.
Israel-based Cellebrite, a subsidiary of Japan’s Sun Corporation, markets forensic tools which empower authorities to bypass passwords on digital devices, allowing them to download, analyse, and visualise data.
Its products are in wide use across the world: a 2019 marketing…
Content Type: News & Analysis
Palantir and the UN’s World Food Programme (WFP) are partnering for a reported $45 million. Palantir, a US-based company that sells data software and has been the centre of numerous scandals.
The World Food Programme provides assistance in food and nutrition to around 92 million people each year. Systems that are produced in agreements such as the one between WFP and Palantir increase risks to the people the they are attempting to help. There are risks to both individuals and whole populations…
Content Type: News & Analysis
European leaders met last week in Brussels to discuss what is supposed to be two separate issues, the next trillion euro-plus budget and migration. In truth, no such separation exists: driven by nationalists and a political mainstream unable to offer any alternative but to implement their ideas, the next budget is in fact all about migration.
This strategy contained within the budget will get the approval of Hilary Clinton, who recently told the Guardian that ‘Europe needs to get a handle on…
Content Type: Advocacy
Image source
The EU extensively bolsters the surveillance and border control capabilities of governments around the world – and is set to dramatically increase such support. Below, we look at how some of these existing funds are being used, how their proposed expansion will undermine people’s privacy around the world for decades to come, and what needs to be done about it.
Migration has dominated the recent EU agenda and will once again be central during this week’s European Council meeting…
Content Type: Long Read
Privacy International’s new report shows how countries with powerful security agencies are training, equipping, and directly financing foreign surveillance agencies. Driven by advances in technology, increased surveillance is both powered by and empowering rising authoritarianism globally, as well as attacks on democracy, peoples’ rights, and the rule of law.To ensure that surveillance powers used by governments are used to protect rather than endanger people, it is essential that the public,…
Content Type: Long Read
Privacy International (PI) has today released a new report, 'Teach 'em to Phish: State Sponsors of Surveillance', showing how countries with powerful security agencies are training, equipping, and directly financing foreign surveillance agencies.
Spurred by advances in technology, increased surveillance is both powered by and empowering rising authoritarianism globally, as well as attacks on democracy, rights, and the rule of law.
As well as providing a background to the issue, the report…
Content Type: Advocacy
A new Privacy International report, based on an international collaborative investigation carried out by 40 NGOs in 42 countries, has found alarming weaknesses in the oversight arrangements that are supposed to govern the sharing of intelligence between state intelligence agencies. Privacy International urges governments to enact urgent reforms and improve public understanding about the scope of intelligence sharing and the safeguards and oversight currently in place.
Content Type: Report
‘Secret Global Surveillance Networks’ is a major PI report, based on an unprecedented international collaborative investigation carried out by 40 NGOs in 42 countries.
Our research shows that, globally, the sharing of intelligence is alarmingly under-regulated, opening the door to human rights abuses. Intelligence sharing has evolved dramatically with the rise of new surveillance technologies, enabling governments to collect, store, and share vast troves of personal information, including data…
Content Type: Long Read
This piece was originally published in Lawfare in April 2018
The United States is party to a number of international intelligence sharing arrangements—one of the most prominent being the so-called “Five Eyes” alliance. Born from spying arrangements forged during World War II, the Five Eyes alliance facilitates the sharing of signals intelligence among the U.S., the U.K., Australia, Canada and New Zealand. The Five Eyes countries agree to exchange by default all signals intelligence…